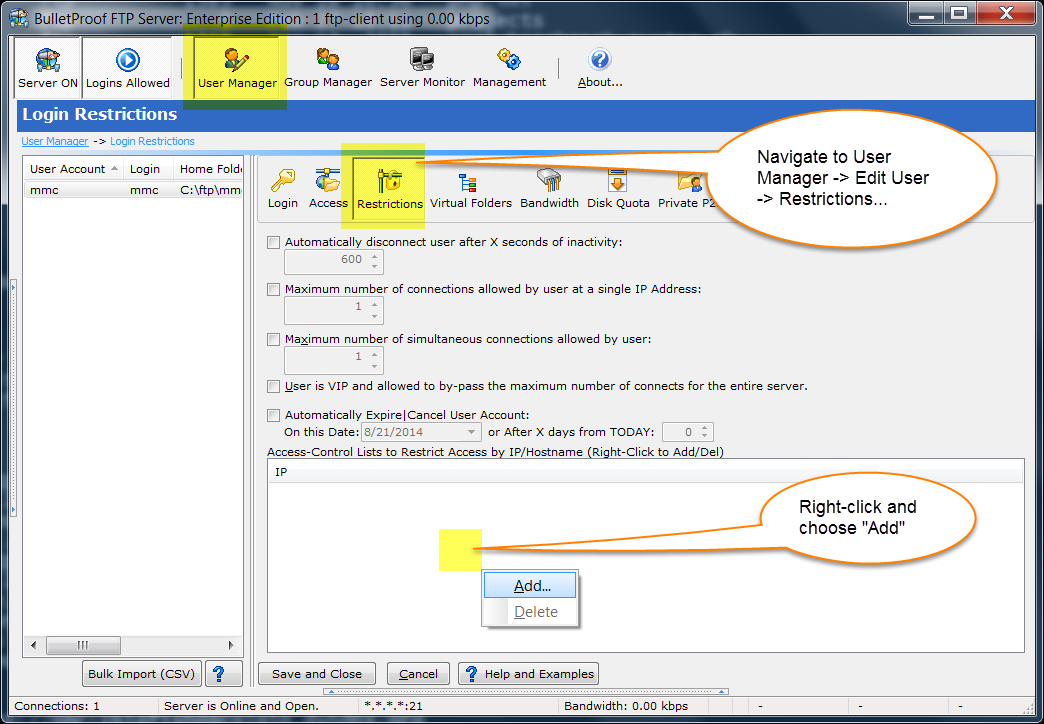
– Right-click and choose “Add IP/ACL”
PLEASE NOTE: All rules should be added as a DENY rule (“-” minus) sign. Entering a ALLOW rule (“+” plus) will override the default rule of “+*.*.*.*” and turn IP/ACL into whitelist only, where all IPs are rejected unless an ALLOW rule is created.
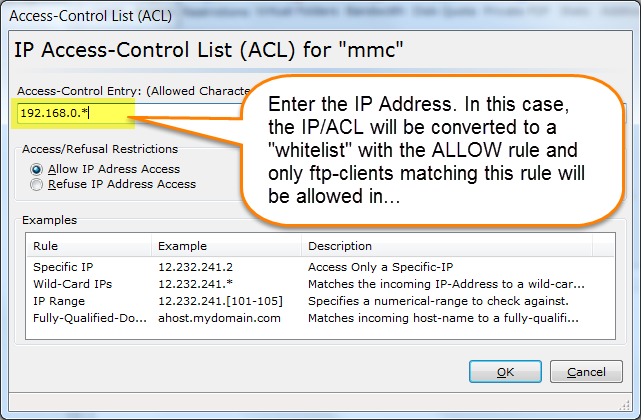
PLEASE NOTE: All rules should be added as a DENY rule (“-” minus) sign. Entering a ALLOW rule (“+” plus) will override the default rule of “+*.*.*.*” and turn IP/ACL into whitelist only, where all IPs are rejected unless an ALLOW rule is created.
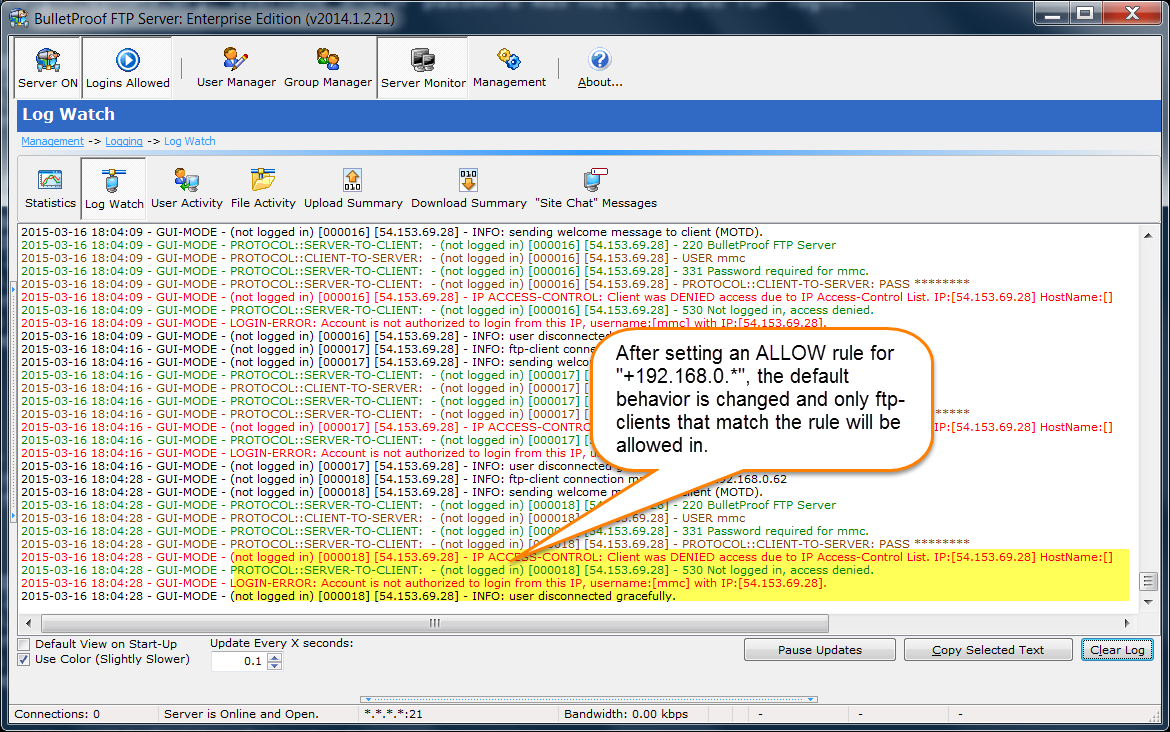
In this example, you’ll see the ftp-client from “-54.153.69.28” is denied. This is because the IP/ACL was converted to a “whitelist” with a single ALLOW rule and “+192.168.0.*” does not match the incoming ftp-client.